OSINT - Simple tips #4 - Usernames
Jan 13, 2021 by Alexandre Croix | 5773 views
This new post on the OSINT field will discuss usernames.
Currently, on the Internet, many websites provide the possibility to create (or even require) a user account. On some of these websites, some user account data is publically available, that can be interesting for an OSINT analyst or hacker.
On the majority of these websites, it is possible to create an account with a username, it is not necessary to use your real name/identity. But a lot of people use the same username (or with small variations) for all accounts. This behaviour will help us to find potential accounts related to a specific person.
From an OSINT point of view, it is important to find the different websites on which our target has an account. It may seem challenging (or at least tedious) to discover all these sites. Fortunately, some tools help us to automatize the research.
namechk.com
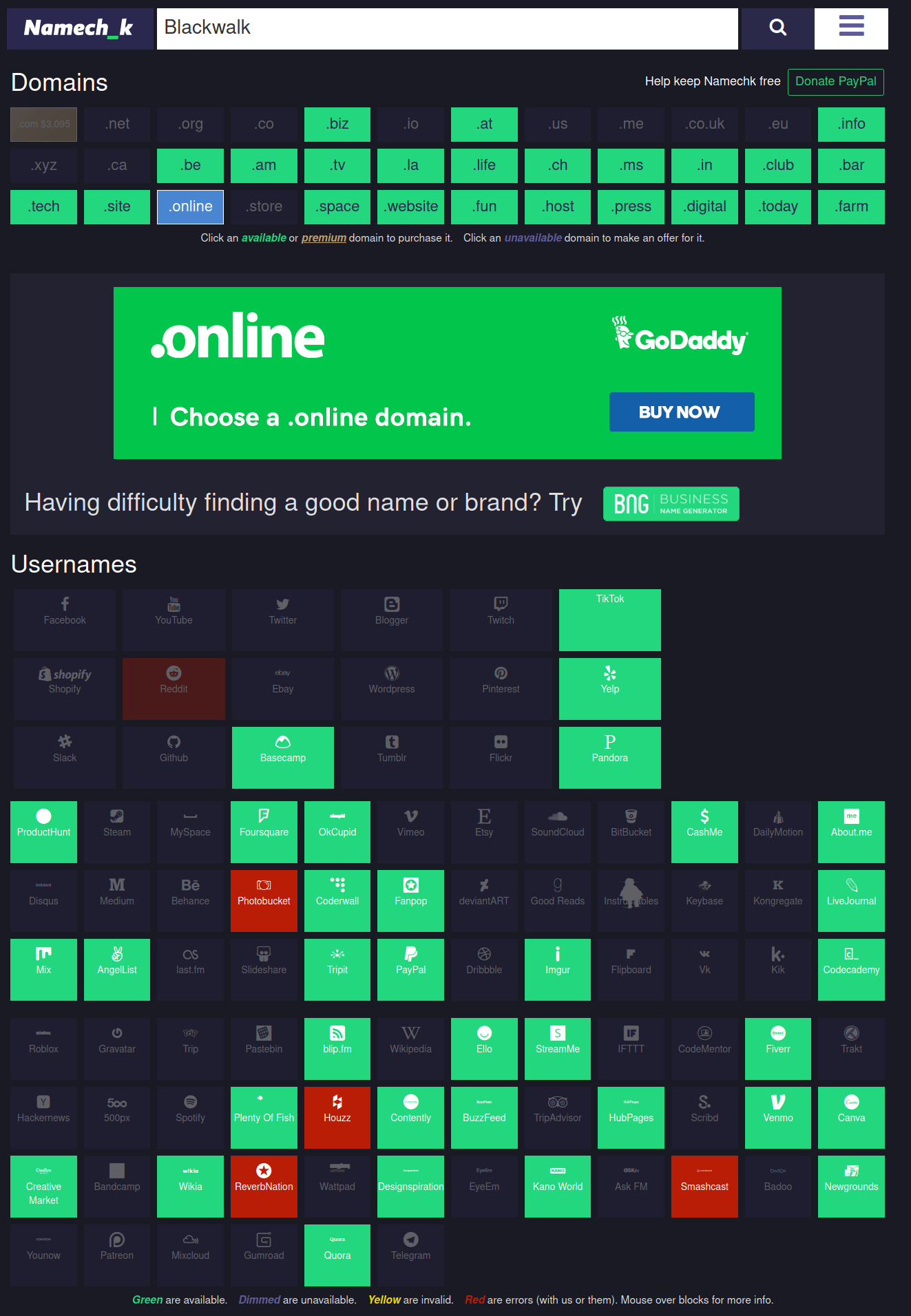
Namechk.com is a website that automatically checks if a username is already used on different websites. You can enter a username, and namechk.com will check on several other sites if an account exists with the same username.
This previous figure is an example with the username blackwalk. All the green cases are websites with blackwalk username available. As an OSINT analyst, we are looking for grey/blue cases.
checkuser.org
As namechk.com, checkuser.org checks the availability of a username on several websites.
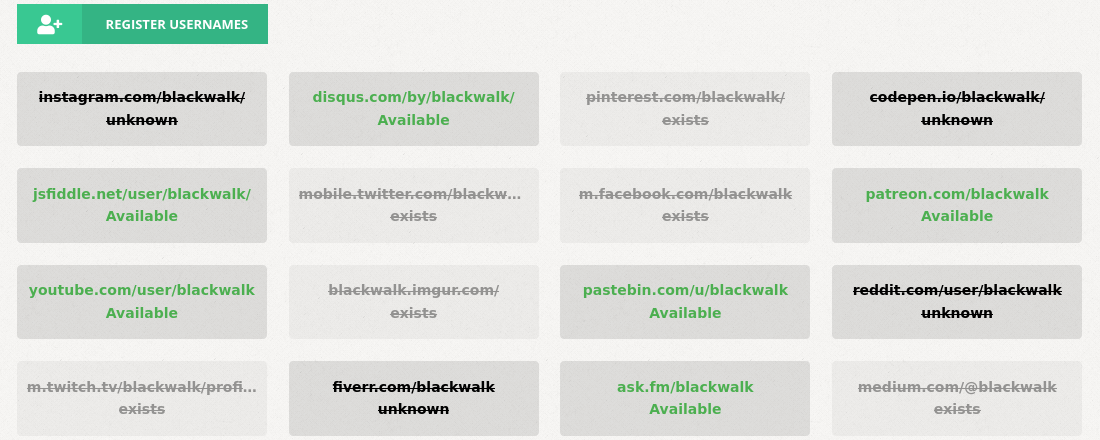
On this second website, the websites on which the username is already used is written. The available sites are in green.
WhatsMyName
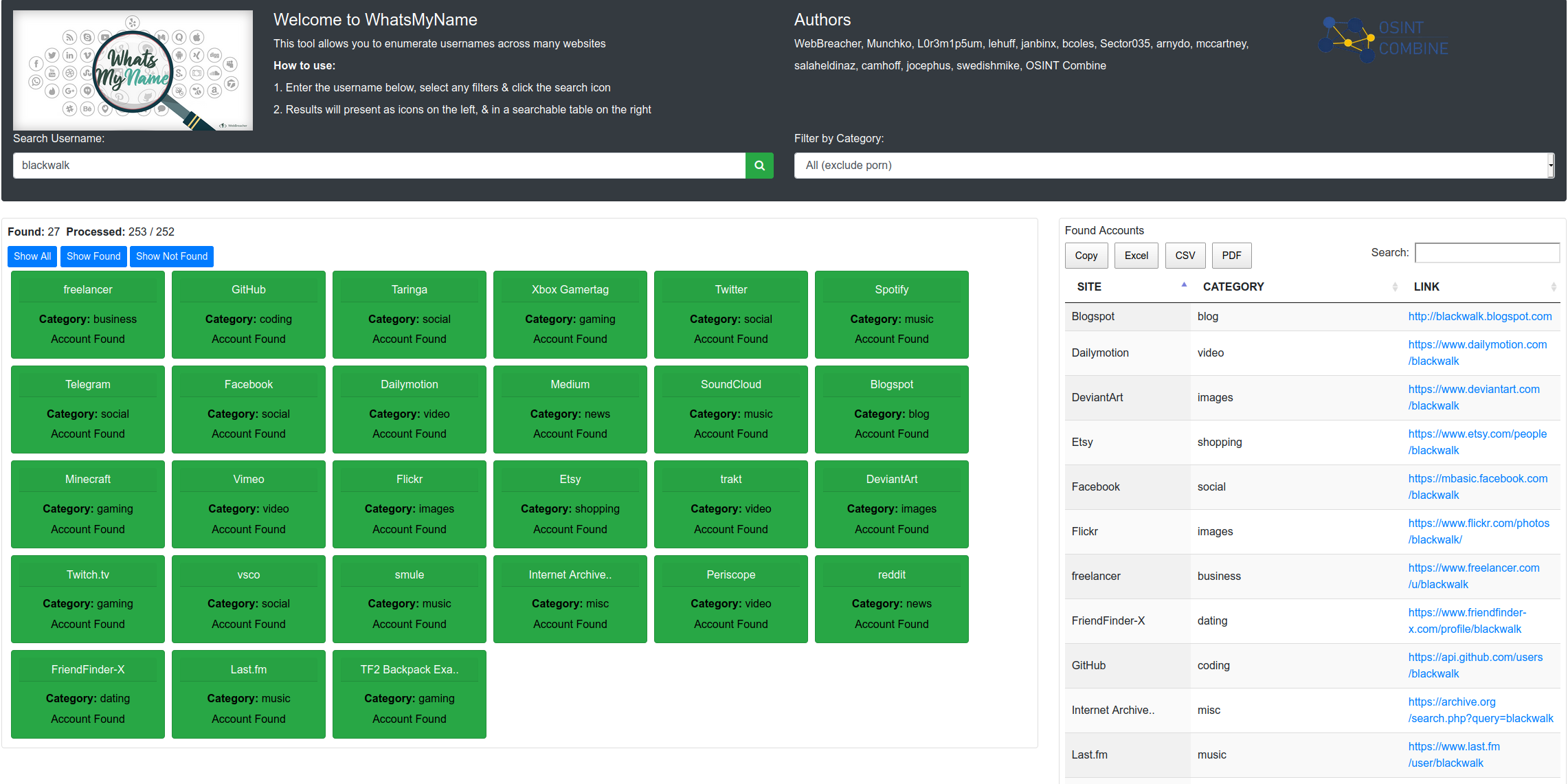
Another great tool to find account is the WhatsMyName project. This project was created by Micah Hoffman. He discovered many URLs where username enumeration was possible: the username appears directly in the address.
The project consists of a JSON file containing information about website/username and answer produces by the website if the username exists or if not.
The following code is a part of the JSON file:
{
"name" : "buymeacoffee",
"check_uri" : "https://www.buymeacoffee.com/{account}",
"account_existence_code" : "200",
"account_existence_string" : "Share with your friends",
"account_missing_string" : "It returned a 404 error.",
"account_missing_code" : "404",
"known_accounts" : ["john","bob"],
"category" : "finance",
"valid" : true
},
{
"name" : "championat",
"check_uri" : "https://www.championat.com/user/{account}/",
"account_existence_code" : "200",
"account_existence_string" : "Личный профил",
"account_missing_string" : "Извините, Ð·Ð°Ð¿Ñ€Ð°ÑˆÐ¸Ð²Ð°ÐµÐ¼Ð°Ñ Ñтраница не найдена",
"account_missing_code" : "404",
"known_accounts" : ["john", "bob"],
"category" : "news",
"valid" : true
},
{
"name" : "Cloudflare",
"check_uri" : "https://community.cloudflare.com/u/{account}",
"account_existence_code" : "200",
"account_existence_string" : "- Cloudflare Community",
"account_missing_string" : "Oops! That page doesn’t exist or is private.",
"account_missing_code" : "404",
"known_accounts" : ["john", "red"],
"category" : "tech",
"valid" : true
},
The advantage of this project: it is easily scriptable and integrable in other tools. You can write your own Ruby, Python, Bash script to test some usernames with some variations. For example, it is possible to test the username blackwalk, BlackWalk or Blackwalk on all the websites in the list very quickly. It is
The file is already integrated with some well-known tool: SpiderFoot (Account Module), Recon-ng (Profile Module). OsintCombine provides a web tool: https://whatsmyname.app/ that uses the WhatsMyName file to check accounts.
Conclusion
If you want to protect your privacy, it is recommended to use a different username for a different website. In practice, it is difficult and tedious. You can use a password manager to help you to remember all your different usernames.
Next week, we will talk about e-mail addresses. Stay tuned!
This blog post is licensed under
CC BY-SA 4.0