Test your Laravel project with GitLab
Oct 2, 2020 by Thibault Debatty | 5811 views
https://cylab.be/blog/95/test-your-laravel-project-with-gitlab
So you have a Laravel project, and as a good programmer you are using GitLab to manage your code, and you started implementing some phpunit tests. But how to run these tests in GitLab?
env.gitlab
First, you’ll need a custom .env file that will be used for the tests. Let’s call it env.gitlab. Here is a starting point that you can tweak to your needs.
APP_NAME="My awesome app"
APP_ENV=test
APP_KEY=base64:/nTMW3a12345678901234567890Ecv/ALCcT+TbaVU4=
APP_DEBUG=true
APP_URL=http://172.0.0.1:8000
LOG_CHANNEL=stack
DB_CONNECTION=sqlite
DB_DATABASE=db.sqlite
BROADCAST_DRIVER=log
CACHE_DRIVER=file
QUEUE_CONNECTION=sync
SESSION_DRIVER=file
SESSION_LIFETIME=120
REDIS_HOST=127.0.0.1
REDIS_PASSWORD=null
REDIS_PORT=6379
MAIL_MAILER=log
EMAIL_VERIFICATION_EXPIRATION_TIME=60
APP_TIMEZONE="Europe/Brussels"
The main attention points here are:
- APP_DEBUG is true so we get some feedback if the tests fail
- DB_CONNECTION is sqlite so we don’t need to setup a MySQL database for the tests
- QUEUE_CONNECTION is sync so we don’t need an external process to run our queue jobs
- MAIL_MAILER is log, so the mails are simply written to the log file, and not sent for real…
.gitlab-ci.yml
Now we can create the file .gitlab-ci.yml (don’t forget the leading dot) that will instruct GitLab how to test our app. Once again, here is a starting point:
# this docker image contains PHP 7.4, composer and some other goodies
# you can find the full recipe (Dockerfile) here
# https://gitlab.cylab.be/cylab/docker/php
image: cylab/php:7.4
test:
before_script:
# use our custom .env file
- cp env.gitlab .env
# install the application
- COMPOSER_CACHE_DIR=composer-cache composer install
- php artisan key:generate
- touch storage/app/db.sqlite
- php artisan migrate
# Optionally, we can install nodejs to build our js and css files
- curl -sL https://deb.nodesource.com/setup_10.x | bash -
- apt install nodejs -y
- npm install
- npm run prod
# run the tests
script:
- vendor/bin/phpunit
# what we want to store locally to speed up the next run of this job
cache:
paths:
- composer-cache/
- node_modules/
In this file:
- We use a Docker image cylab/php:7.4 that contains PHP 7.4 (obviously) but also some additional modules and goodies.
- There is only one job called test, to keep our pipeline clean and fast. We can define multiple jobs and stages if we need to run the tests with different Docker images, for example to test with different versions of PHP…
- We instruct composer to use a custom directory to store downloaded libraries (namely
composer-cache) and put these files in cache, so they can be reused at the next execution of the job. This allows to reduce the amount of downloaded libraries. Other files like bootstrap are not put in cache because these would simply pollute the next execution of the job and might corrupt the results of the tests.
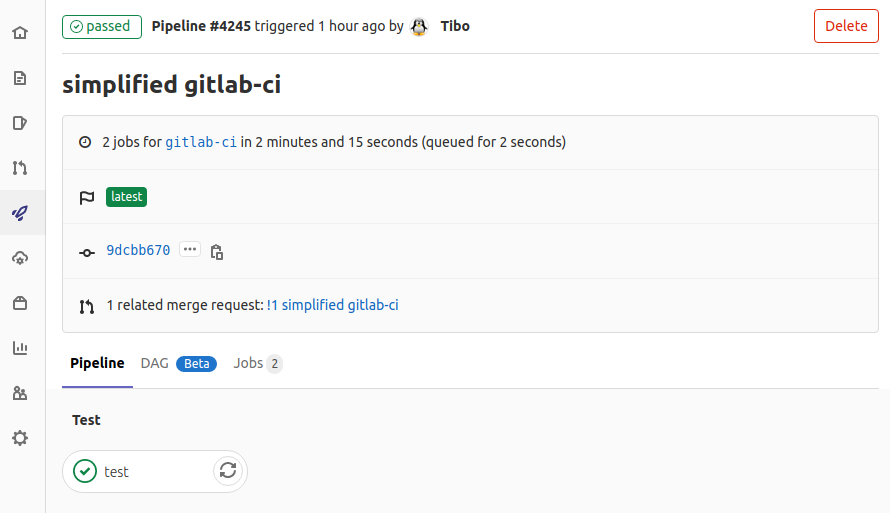
commit and push
Finally, we can commit and push this all to GitLab:
git add env.gitlab
git add .gitlab-ci.yml
git commit -m "test with gitlab"
git push
Once this basic tests are configured, don’t hesitate to add:
This blog post is licensed under
CC BY-SA 4.0